DNS hasn’t changed all that much since Paul Mockapetris invented it in 1983. It still addresses exactly the same requirement stated in RFC 882:
As applications grow to span multiple hosts, then networks, and finally internets, these applications must also span multiple administrative boundaries and related methods of operation (protocols, data formats, etc.).The number of resources
(for example mailboxes), the number of locations for resources, and the diversity of such an environment cause formidable problems when we wish to create consistent methods for referencing particular resources that are similar but scattered throughout the environment.
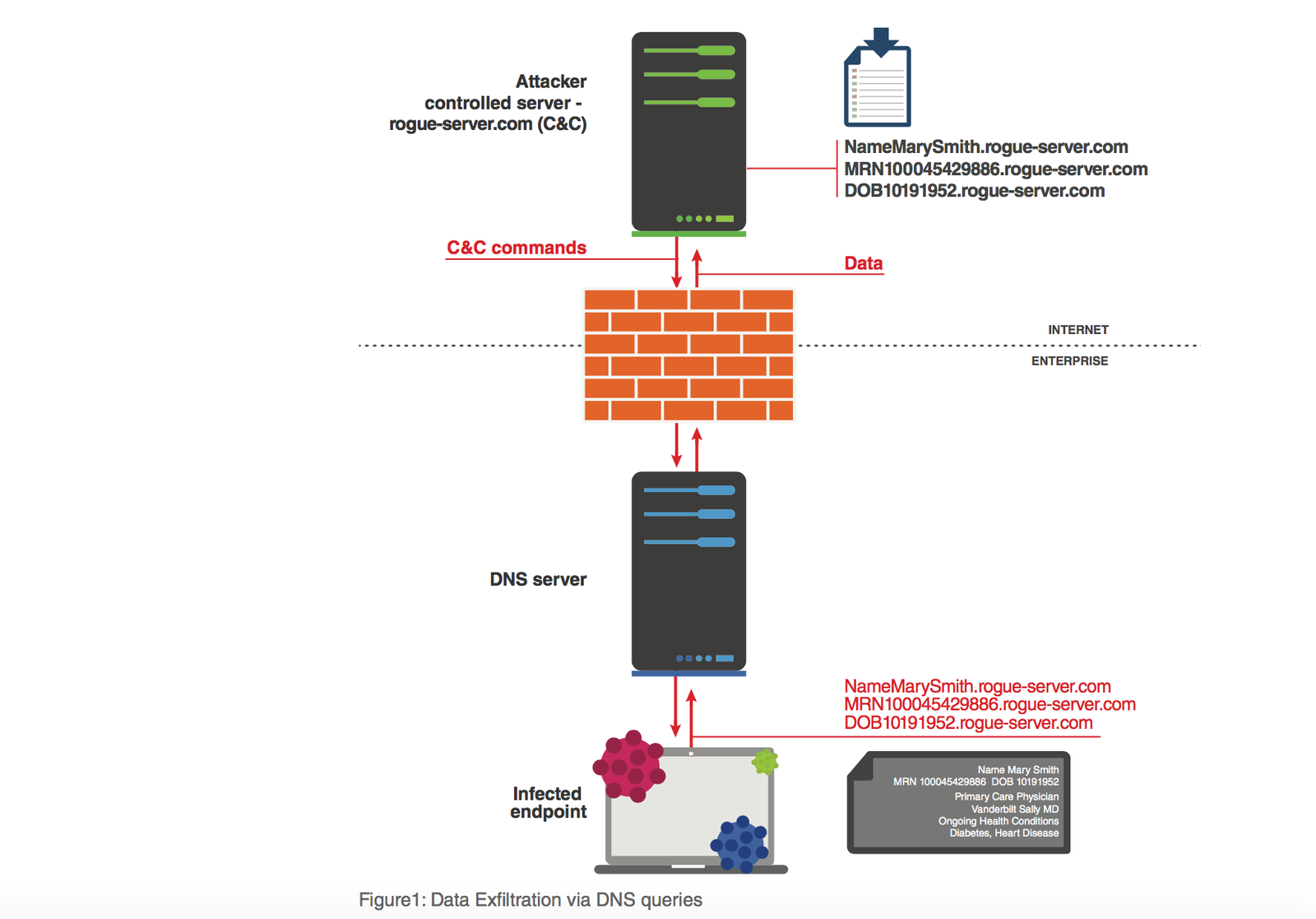
According to Dan Kaminsky, the famous DNS security researcher, DNS can be thought of as a globally deployed routing and caching overlay network that connects both public and private Internet, which raises serious questions: Is it sufficiently secure? Is it vulnerable to data breaches? The answer is that DNS can be abused in all sorts of unconventional ways that make it the perfect back door for hackers seeking to steal sensitive data.
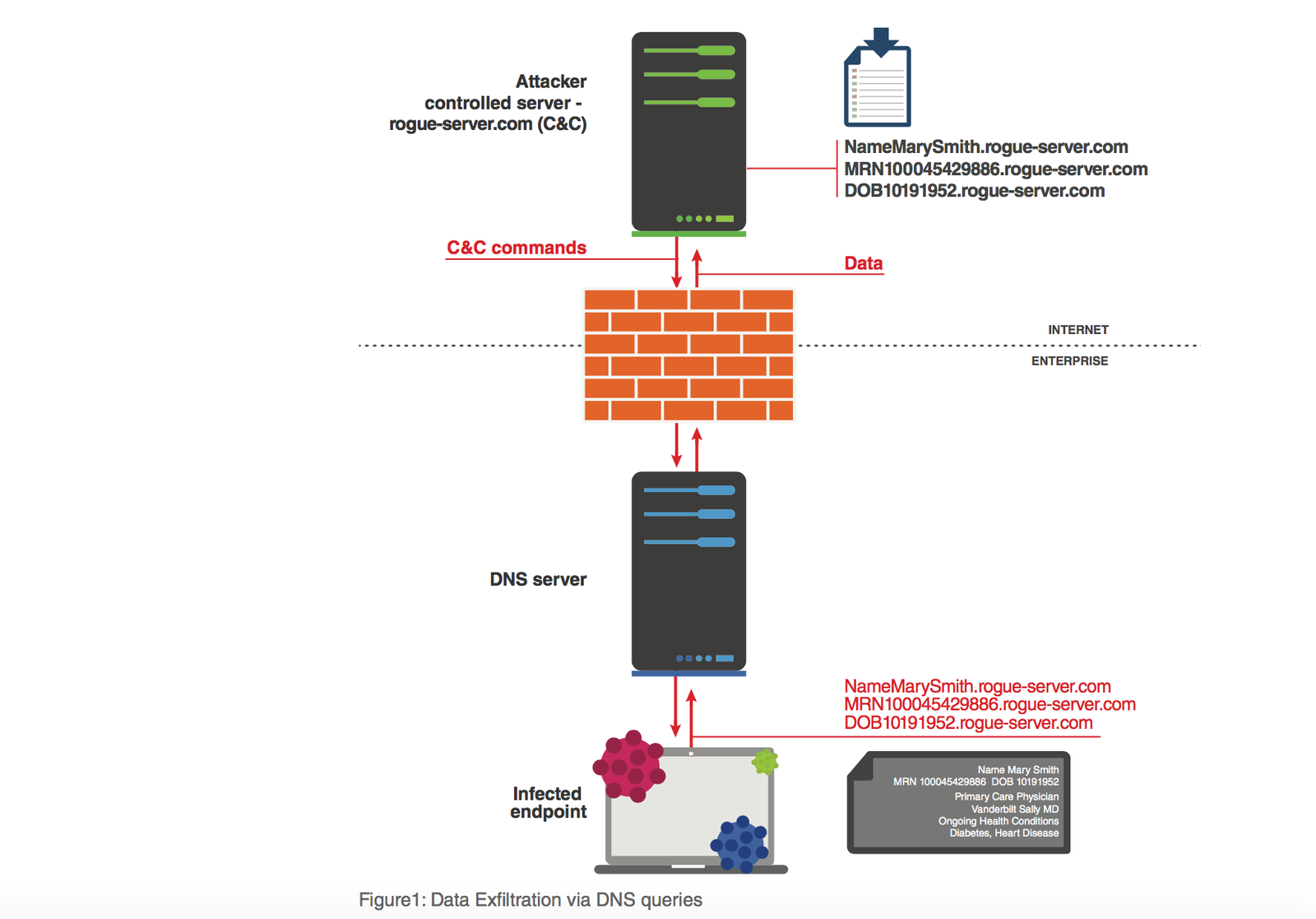
This paper lays out the tactics hackers use to exploit DNS for purposes of DNS tunneling and data exfiltration. It also introduces Infoblox’s new and patented capability—Infoblox DNS Threat Analytics—which uses machine learning and performs real-time analytics on live DNS queries to detect and automatically block DNS tunneling and data exfiltration.
[button href=”http://channelpostmea.com/wp-content/uploads/2017/08/infoblox-whitepaper-data-exfiltration-and-dns-closing-the-back-door.pdf” target=”1″ bg_color=”#222″ bg_hover=”#555″ text_color=”” text_hover=”#fff”]Download the Whitepaper[/button]